Last Updated: March 2026
This page is updated monthly. Check back for newly disclosed vulnerabilities.
Vue 2 EOL Status
End of Life (Dec 31, 2023)
Executive Summary for Security Teams
Vue 2 reached End of Life on December 31, 2023. Since then, no security patches have been released by the Vue core team. While Vue 2 core has had relatively few direct CVEs, the primary risk is:
- 1. Future vulnerabilities will not be patched — Any new CVE discovered in Vue 2 will remain unpatched indefinitely.
- 2. Ecosystem dependencies are also EOL — Vue 2-specific libraries (Vuetify 2, BootstrapVue, etc.) are no longer maintained.
- 3. Compliance frameworks flag EOL software — SOC 2, HIPAA, PCI-DSS auditors will cite Vue 2 as a finding.
For compliance implications, see our detailed guide: Your Next Compliance Audit Will Fail.
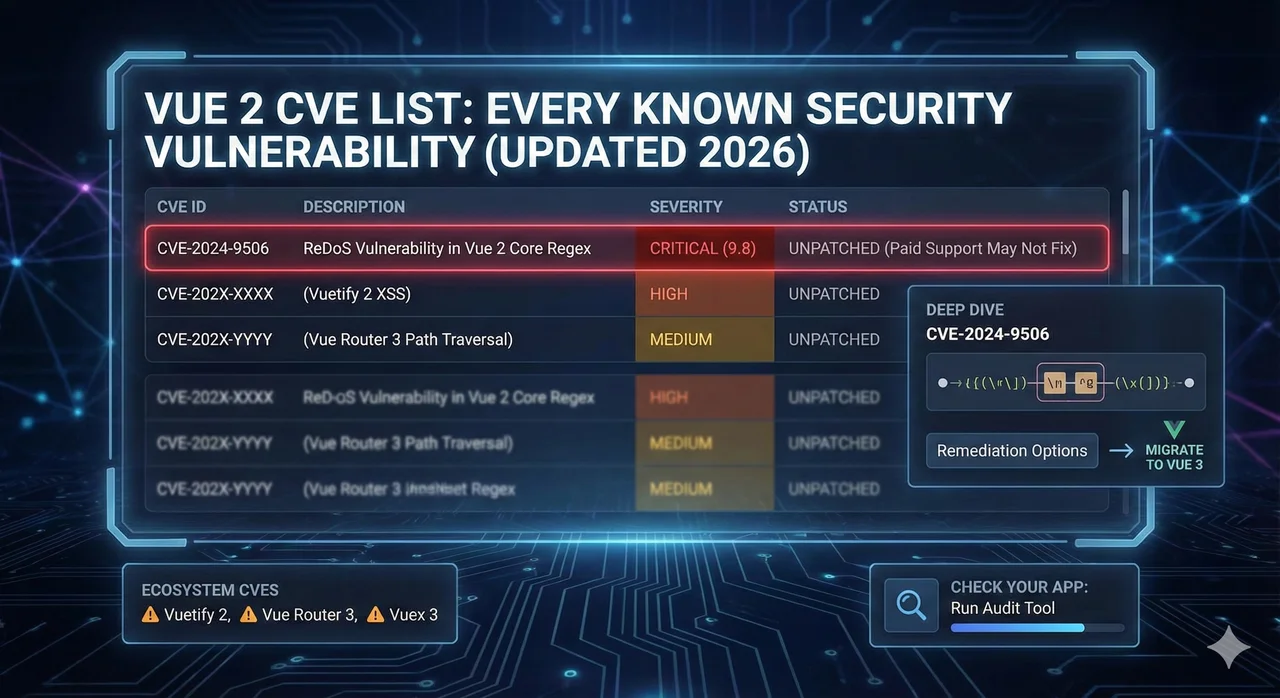
Vue 2 Core Vulnerabilities
Vue.js core has maintained a relatively strong security record. The following CVEs have been publicly disclosed for Vue 2:
CVE-2024-6783
ReDoS in parseHTML function
Affected Versions
Vue 2.0.0 - 2.7.16
CVSS Score
5.3 (Medium)
Description
A Regular Expression Denial of Service (ReDoS) vulnerability exists in the parseHTML function used during template compilation. Maliciously crafted templates can cause excessive CPU consumption.
Remediation
No patch available — Migrate to Vue 3
CVE-2018-11235 (Indirect)
Prototype Pollution via vue-template-compiler
Affected Versions
Vue 2.x with vulnerable dependencies
CVSS Score
7.8 (High)
Description
While not in Vue core itself, older versions of vue-template-compiler used dependencies vulnerable to prototype pollution attacks. This affects build-time compilation.
Remediation
Update to Vue 2.7.x or migrate to Vue 3
Why Vue 2 Core Has Few Direct CVEs
Vue.js is primarily a client-side framework. Most severe CVEs affect server-side code where attackers can execute arbitrary code. Vue's template compilation happens at build time (not runtime), reducing attack surface. However, this doesn't mean Vue 2 applications are secure—the ecosystem and dependencies are where most vulnerabilities exist.
Vue 2 Ecosystem Vulnerabilities
The greater risk lies in Vue 2's ecosystem—libraries that only support Vue 2 and are no longer maintained:
Vuetify 2.x
Multiple XSS and DOM manipulation vulnerabilities
Vuetify 2 is no longer maintained. Several components had XSS vulnerabilities in user-supplied content handling. The v-html directive usage in Vuetify components created injection risks.
Status: No further patches. Migrate to Vuetify 3.
BootstrapVue
Inherited Bootstrap 4 vulnerabilities
BootstrapVue wraps Bootstrap 4, which is also EOL. Known vulnerabilities in Bootstrap's JavaScript components (modal, tooltip, etc.) are present in BootstrapVue and will never be patched.
Status: Project abandoned. See BootstrapVue alternatives.
Vue Router 3.x
Open redirect vulnerabilities
Older versions of Vue Router 3 had open redirect vulnerabilities in route handling. While patched in later 3.x versions, new vulnerabilities discovered post-EOL will not receive fixes.
Status: Update to latest 3.x, plan migration to Router 4.
Vuex 3.x
Maintenance mode only
Vuex is in maintenance mode—no new features, only critical bug fixes. The Vue team recommends migrating to Pinia, which has active security maintenance.
Status: Migrate to Pinia.
High-Risk Transitive Dependencies
Vue 2 projects typically include these dependencies with known vulnerabilities. Run npm audit to check your project.
| Package | Common CVEs | Severity | Fix |
|---|---|---|---|
| lodash | Prototype Pollution (CVE-2020-8203) | Critical | Update to 4.17.21+ |
| node-sass | Multiple libsass CVEs | High | Replace with sass |
| webpack-dev-server (v3) | Path traversal, SSRF | High | Update to v4+ |
| serialize-javascript | RCE (CVE-2020-7660) | Critical | Update to 3.1.0+ |
| minimist | Prototype Pollution (CVE-2021-44906) | High | Update to 1.2.6+ |
| postcss (v7) | ReDoS (CVE-2021-23382) | Medium | Update to v8+ |
Run This Command
npm audit --productionThis shows vulnerabilities in your production dependencies. For full audit including dev dependencies: npm audit
The Real Risk: Future Unknown Vulnerabilities
The CVEs listed above are known vulnerabilities. The greater risk is unknown future vulnerabilities.
If Vue 3 gets a CVE
The Vue team releases a patch within days. You update and you're protected.
If Vue 2 gets a CVE
No patch will be released. You're vulnerable indefinitely unless you migrate or purchase extended support.
Historical CVE Discovery Rates
JavaScript frameworks typically see 2-5 CVEs per year on average. Even mature, well-audited frameworks like React and Angular continue to have vulnerabilities discovered years after release.
It's not a question of if Vue 2 will have more CVEs—it's when. And when that happens, you'll have two choices: pay for extended support (like HeroDevs NES) or accept the vulnerability.
Compliance Impact of Vue 2 CVEs
For regulated industries, the presence of unpatched CVEs—or the potential for unpatched CVEs—is a compliance finding:
SOC 2 Type II
CC7.1 requires timely vulnerability management. EOL software with no patch path fails this control automatically.
PCI-DSS 4.0
Requirement 6.3.3 mandates patching known vulnerabilities within defined timeframes. No patches = automatic failure.
HIPAA Security Rule
§164.308(a)(5)(ii)(B) requires protection against malicious software. EOL components are a cited deficiency.
FedRAMP
High vulnerabilities must be patched in 30 days. With EOL software, this is impossible—authorization at risk.
For detailed compliance implications, see: Your Next Compliance Audit Will Fail.
Remediation Options
Migrate to Vue 3 (Recommended)
The permanent solution. Vue 3 is actively maintained with regular security patches. Migration eliminates the EOL risk entirely.
Extended Support (Temporary)
Services like HeroDevs NES provide security patches for Vue 2. This buys time but doesn't solve the underlying problem—you'll still need to migrate eventually.
Read: The Extended Support Trap →Accept the Risk (Not Recommended)
Document the risk, get sign-off from security leadership, and accept potential compliance findings. This is only viable for internal tools with no sensitive data and no compliance requirements.
How to Monitor for New Vue 2 CVEs
If you must stay on Vue 2 temporarily, set up monitoring for new vulnerabilities:
Subscribe to NVD alerts
Set up email alerts at nvd.nist.gov for "vue" keyword.
Enable Dependabot/Snyk
Automated dependency scanning catches vulnerabilities in your supply chain.
Run npm audit weekly
Add npm audit to your CI pipeline. Fail builds on high/critical findings.
Bookmark this page
We update this CVE list monthly with newly disclosed vulnerabilities.
Need a Security-Focused Migration Plan?
Our Migration Readiness Audit includes a complete vulnerability assessment of your Vue 2 application—direct CVEs, ecosystem risks, and dependency issues. Get a remediation plan and fixed-price migration quote.
✓ Full dependency audit ✓ CVE remediation plan ✓ Compliance documentation
Conclusion
Vue 2's direct CVE count is relatively low, but that's not the full picture. The ecosystem vulnerabilities, transitive dependencies, and—most importantly—the certainty of future unpatched CVEs make Vue 2 a security liability.
For security teams, the recommendation is clear: migrate to Vue 3 or implement extended support as a bridge solution. Running unpatched EOL software is an unnecessary risk that compliance frameworks will flag.
This page will be updated monthly with newly disclosed CVEs. Bookmark it as a reference for your security audits and compliance documentation.